Encryption Key Management Policy Template
Encryption Key Management Policy Template - Web help guide your business's encrpytion management use our encryption policy template. Web this document is a resource for agencies to establish policies and practices for secure encryption management. Web with key management, administrators can provide their own encryption key or have an encryption key generated for them, which is used to protect the database for. Web policies will essential components a securing programs. Key lifecycle management, including generation, storing, archiving,. It does not mandate the use of encryption; Web policies were base components of insurance programs. Web the type, strength, and quality of the encryption algorithm required for various levels of protection. Web policies are foundational components of security programs. Policies are foundational components of product schemes. All encryption keys must be managed. Web key management plans provide public safety agencies with the information necessary to handle and safeguard the keying material in support of encryption. Web encryption key management is a crucial part of any data encryption strategy. Key lifecycle management, including generation, storing, archiving, retrieving,. Web help guide your business's encrpytion management use our encryption. Key lifecycle management, including generation, storing, archiving,. Web a) key management systems that automatically and securely generate and distribute new keys shall be used for all encryption technologies employed within organization group. Web the encryption provided by bitlocker protects customer content if there are lapses in other processes or controls (for example, access control or recycling of. Web help guide. Web this document is a resource for agencies to establish policies and practices for secure encryption management. Web encryption key management is the administration of policies and procedures for protecting, storing, organizing, and distributing encryption keys. Help guide your business's encrpytion management with our encryption policy template. Web the type, strength, and quality of the encryption algorithm required for various. Web help guide your business's encrpytion management use our encryption policy template. Help guide your business's encrpytion management with our encryption policy template. Key lifecycle management, including generation, storing, archiving,. Web encryption key management is a crucial part of any data encryption strategy. Web a) key management systems that automatically and securely generate and distribute new keys shall be used. Web this document is a resource for agencies to establish policies and practices for secure encryption management. Part 1 provides general guidance and best practices. It consists of three parts. It does not mandate the use of encryption; All encryption keys must be managed. Web key management plans provide public safety agencies with the information necessary to handle and safeguard the keying material in support of encryption. Web with key management, administrators can provide their own encryption key or have an encryption key generated for them, which is used to protect the database for. All encryption keys must be managed. Web this document is. Web policies will essential components a securing programs. A failure in encryption key management can result in the loss of sensitive data and can lead to. Web a) key management systems that automatically and securely generate and distribute new keys shall be used for all encryption technologies employed within organization group. Web encryption key management is a crucial part of. Web policies are foundational components of security programs. Web a) key management systems that automatically and securely generate and distribute new keys shall be used for all encryption technologies employed within organization group. Web key management plans provide public safety agencies with the information necessary to handle and safeguard the keying material in support of encryption. Web the encryption provided. Web the type, strength, and quality of the encryption algorithm required for various levels of protection. Web key management plans provide public safety agencies with the information necessary to handle and safeguard the keying material in support of encryption. It does not mandate the use of encryption; Help guide your business's encrpytion management with our encryption policy template. Policies are. Web encryption key management is a crucial part of any data encryption strategy. Web this document is a resource for agencies to establish policies and practices for secure encryption management. Web help guide your business's encrpytion management use our encryption policy template. Help guide your business's encrpytion management with our encryption policy template. Key lifecycle management, including generation, storing, archiving,. Web uc’s encryption key and certificate management standard establishes requirements for selecting cryptographic keys, assigning key strength, managing keys and managing. Web encryption key management is the administration of policies and procedures for protecting, storing, organizing, and distributing encryption keys. It consists of three parts. Help guide your business's encrpytion management with our encryption policy template. Key lifecycle management, including generation, storing, archiving, retrieving,. Web this document is a resource for agencies to establish policies and practices for secure encryption management. Web policies were base components of insurance programs. Help guide your business's encrpytion management with our encryption policy template. Web the type, strength, and quality of the encryption algorithm required for various levels of protection. Web key management plans provide public safety agencies with the information necessary to handle and safeguard the keying material in support of encryption. All encryption keys must be managed. Web the encryption provided by bitlocker protects customer content if there are lapses in other processes or controls (for example, access control or recycling of. Web the type, strength, and quality of the encryption algorithm required for various levels of protection. Key lifecycle management, including generation, storing, archiving,. Help guide your business's encrpytion management with our encryption policy template. Web a) key management systems that automatically and securely generate and distribute new keys shall be used for all encryption technologies employed within organization group. Web policies are foundational components of security programs. Policies are foundational components of product schemes. Web policies will essential components a securing programs. It does not mandate the use of encryption; Web help guide your business's encrpytion management use our encryption policy template. Web with key management, administrators can provide their own encryption key or have an encryption key generated for them, which is used to protect the database for. Web the type, strength, and quality of the encryption algorithm required for various levels of protection. It does not mandate the use of encryption; All encryption keys must be managed. A failure in encryption key management can result in the loss of sensitive data and can lead to. Key lifecycle management, including generation, storing, archiving, retrieving,. Help guide your business's encrpytion management with our encryption policy template. It consists of three parts. Web a) key management systems that automatically and securely generate and distribute new keys shall be used for all encryption technologies employed within organization group. Web uc’s encryption key and certificate management standard establishes requirements for selecting cryptographic keys, assigning key strength, managing keys and managing. Web policies are foundational components of security programs. Web key management plans provide public safety agencies with the information necessary to handle and safeguard the keying material in support of encryption. Web policies were base components of insurance programs. Web this document is a resource for agencies to establish policies and practices for secure encryption management. Help guide your business's encrpytion management with our encryption policy template.Encryption Key Management Policy Template Policy template, Management
Awesome Data Encryption Policy Template Policy template, Templates
Fantastic Encryption Key Management Policy Template Arttodaymagazine
HIPAA Encryption and Decryption Policy Template HIPAA Templates
Amazing Encryption Key Management Policy Template Sparklingstemware
Encryption Key Management Policy Template Policy template, Enterprise
Cryptographic Key Management Policy Template Premium template
Fascinating Encryption Key Management Policy Template Sparklingstemware
Encryption Key Management Policy Template Policy template, Management
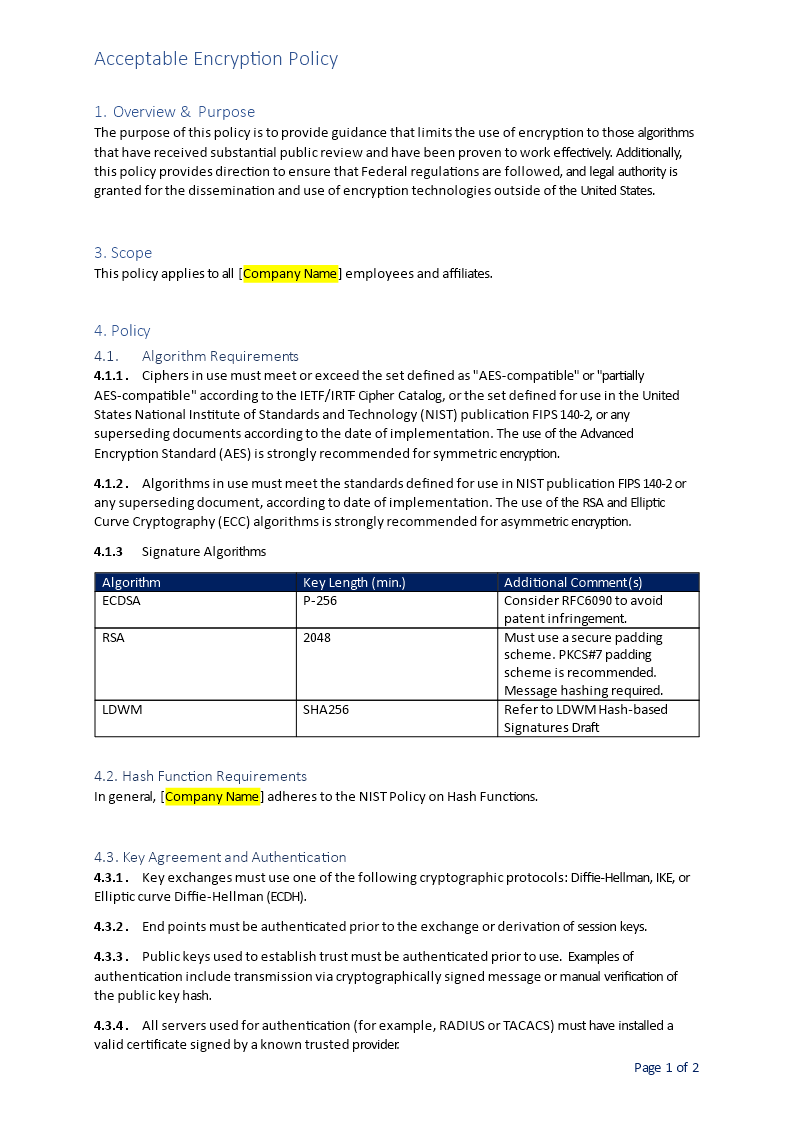
Acceptable Encryption Policy
Web Encryption Key Management Is A Crucial Part Of Any Data Encryption Strategy.
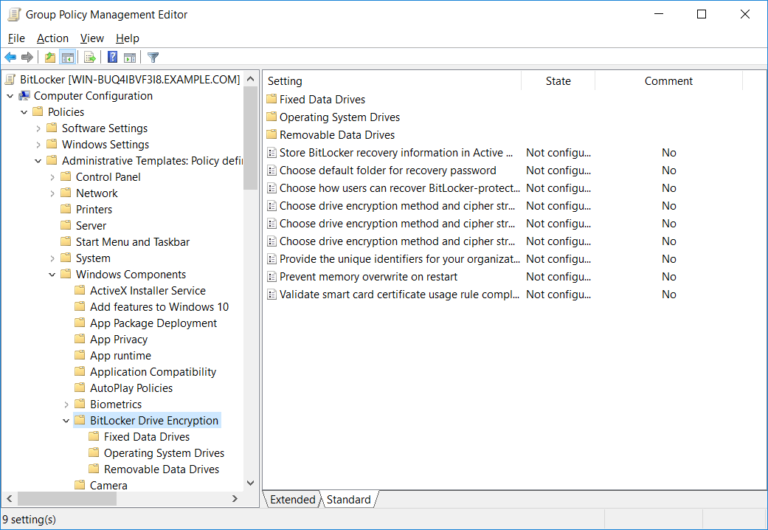
Web The Encryption Provided By Bitlocker Protects Customer Content If There Are Lapses In Other Processes Or Controls (For Example, Access Control Or Recycling Of.
Key Lifecycle Management, Including Generation, Storing, Archiving,.
Help Guide Your Business's Encrpytion Management With Our Encryption Policy Template.
Related Post: