Least Privilege Policy Template
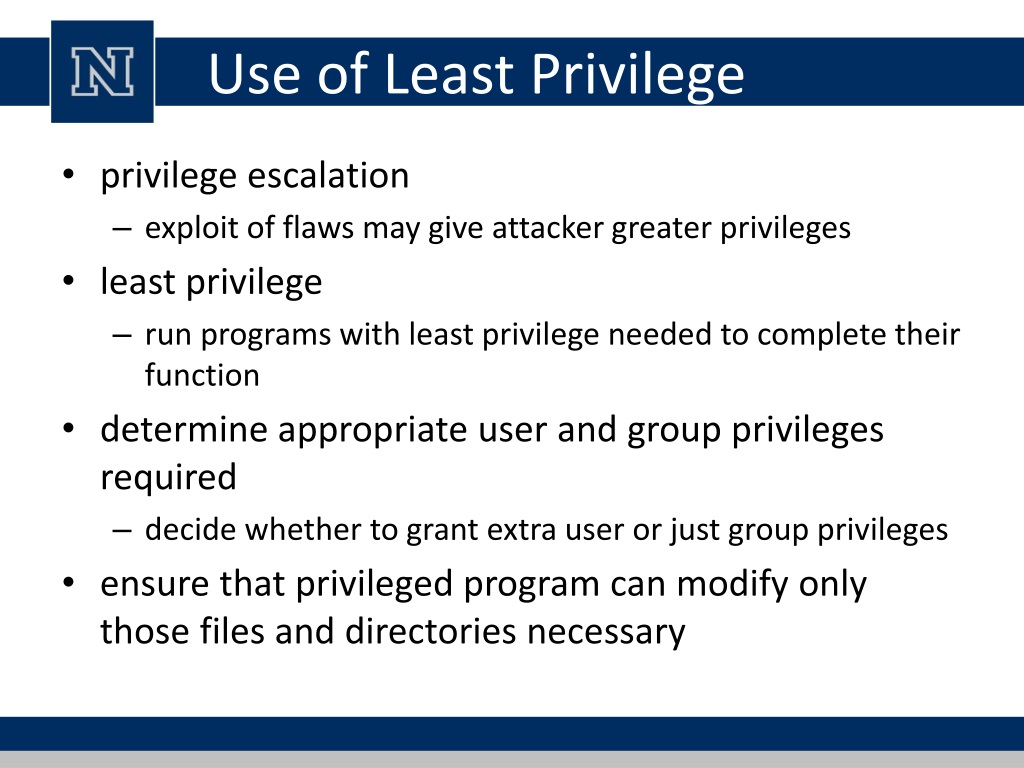
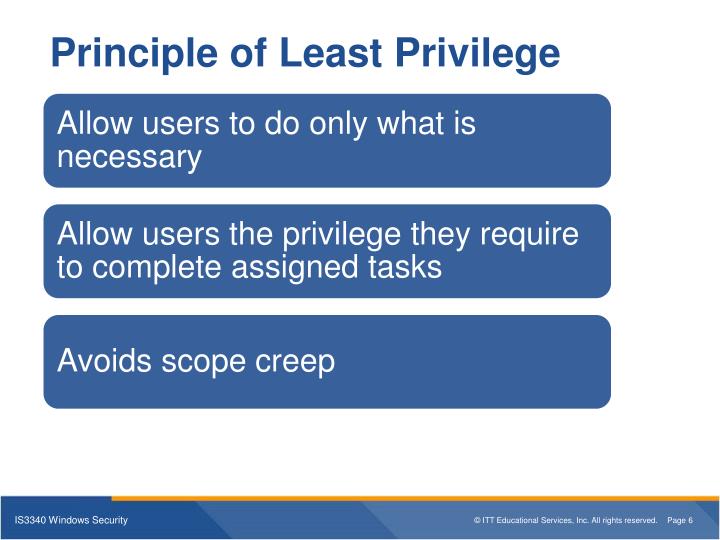
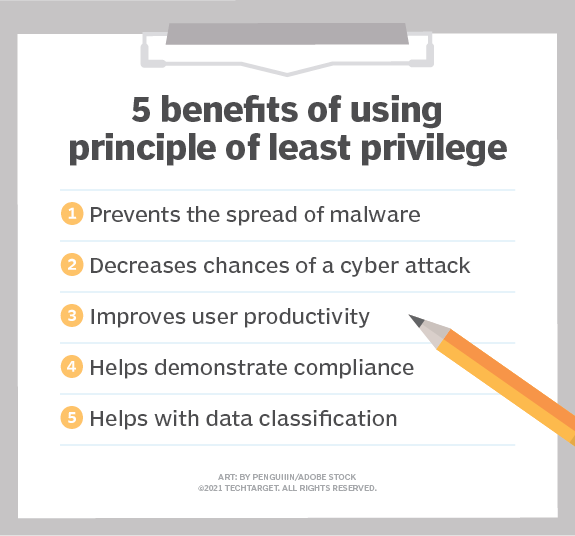
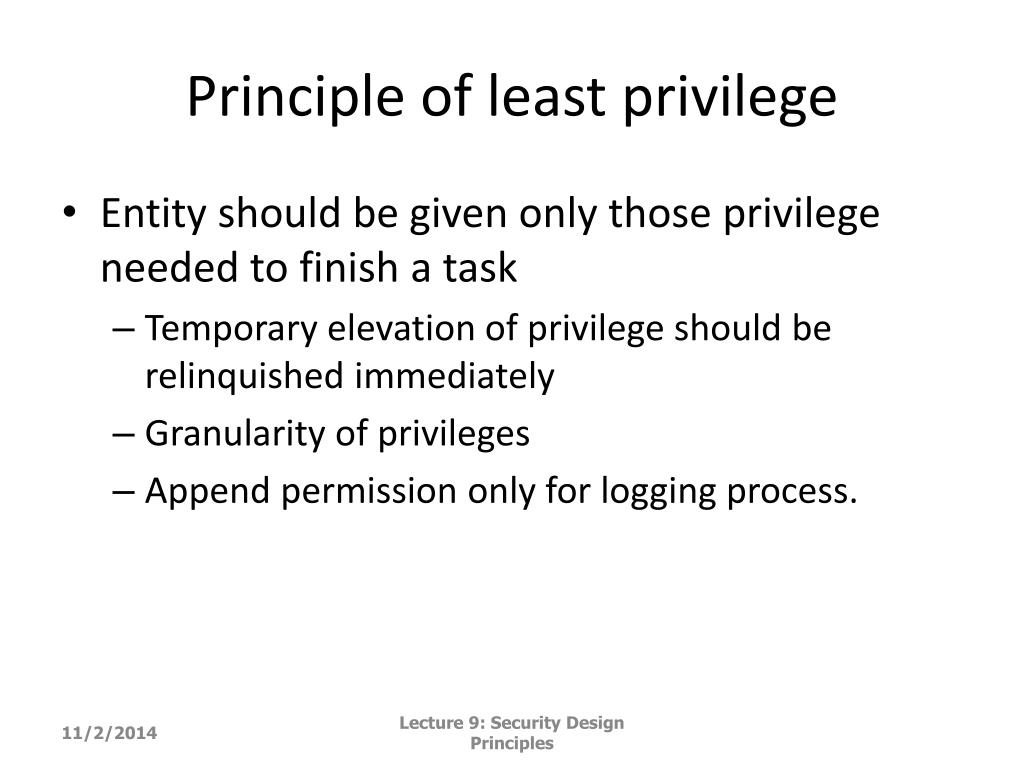
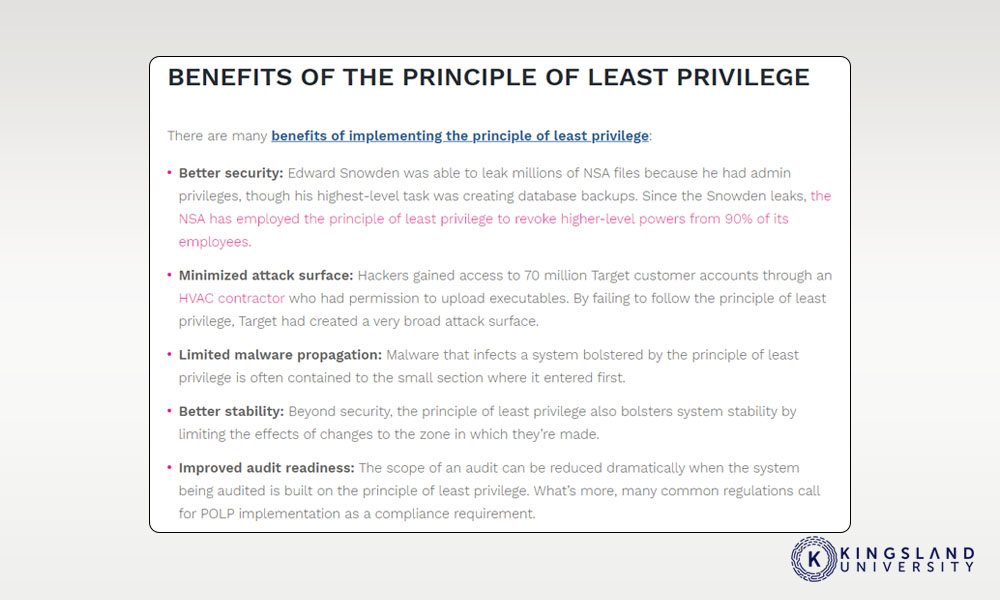
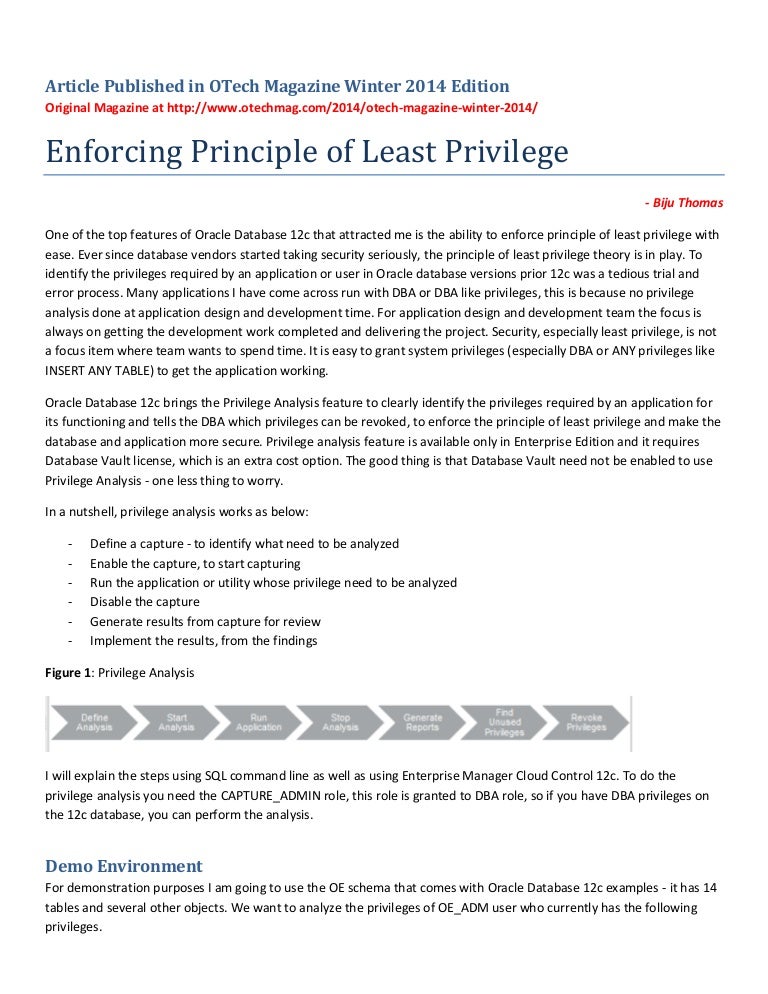
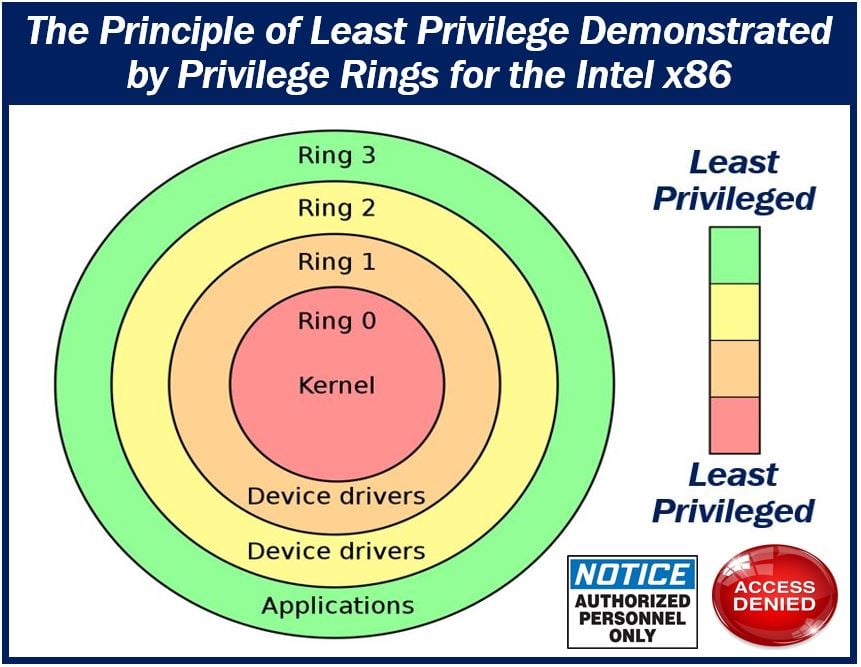
Least Privilege Policy Template - Web the principle of least privilege, or “least privilege access,” is a cyber security best practice that requires limiting users to the privileges necessary to perform a specific task. Web a minimum access policy ensures that users have the lowest level of privileges to complete necessary functions. In this post, i’ve shown two different techniques that you can use to create least privilege policies for iam. Web the principle of least privilege model (also called the principle of minimal privilege or the principle of least authority) is widely considered to be a cybersecurity. You can adapt these methods. Web follow the principle of least privilege to implement a zero trust security strategy never grant broad or standing privileges. The principle of least privilege access is a software security best practice that provides a user only the minimum set of rights required to perform an. Web 19 jan 2022. Web developing an access termination policy for least privilege. Privileged access users must have permissions set to the lowest level of access needed to accomplish their job function. Web the principle of least privilege (polp) the first security principle that i am going to discuss is one that most system administrators are familiar with: The principle of least privilege access is a software security best practice that provides a user only the minimum set of rights required to perform an. Web this guide explains the principle out least. Web the information security principle of least privilege asserts that users and applications should be granted access only to the data and operations they require to. The principle of least privilege access is a software security best practice that provides a user only the minimum set of rights required to perform an. They are based on compliance requirements outlined by. Before using iam, it’s important to. Privileged access users must have permissions set to the lowest level of access needed to accomplish their job function. Web blog what is least privilege & why do you need it? Web a minimum access policy ensures that users have the lowest level of privileges to complete necessary functions. Web the goal of least. In this post, i’ve shown two different techniques that you can use to create least privilege policies for iam. In a least privilege model, privileged users and systems have. What is the principle of least privilege (polp)? Scope these controls apply to information and information processing systems at the. Best practice guide to implementing. Web the information security principle of least privilege asserts that users and applications should be granted access only to the data and operations they require to. Web blog what is least privilege & why do you need it? Web a minimum access policy ensures that users have the lowest level of privileges to complete necessary functions. What is the principle. Web the goal of least privilege enforcement is to give the user the least amount of privilege necessary to get their job done. Web the principle of least privilege, or “least privilege access,” is a cyber security best practice that requires limiting users to the privileges necessary to perform a specific task. In this post, i’ve shown two different techniques. Web applying the principles of least privilege aws identity and access management (iam) is the service used to manage access to aws services. Before using iam, it’s important to. Web the principle of least privilege, or “least privilege access,” is a cyber security best practice that requires limiting users to the privileges necessary to perform a specific task. Web this. Web developing an access termination policy for least privilege. Best practice guide to implementing the least. Web the principle of least privilege must be followed. Scope these controls apply to information and information processing systems at the. Web the principle of least privilege model (also called the principle of minimal privilege or the principle of least authority) is widely considered. Web the principle of least privilege model (also called the principle of minimal privilege or the principle of least authority) is widely considered to be a cybersecurity. Web this guide explains the principle out least privilege perks and how until implement the principle of least privilege (polp). Your organization should also focus on building and maintaining a specific set of. Web this guide explains the principle out least privilege perks and how until implement the principle of least privilege (polp). Best practice guide to implementing. Web the principle of least privilege, or “least privilege access,” is a cyber security best practice that requires limiting users to the privileges necessary to perform a specific task. The principle of least privilege access. They are based on compliance requirements outlined by cis, nist, pci and. You can adapt these methods. Best practice guide to implementing the least. Web this guide explains the principle of least privilege features and how to implement of principle of least privilege (polp). One of the biggest advantages to a least. Least privilege is the concept and practice of restricting. Web the information security principle of least privilege asserts that users and applications should be granted access only to the data and operations they require to. Best practice guide to implementing. Web the principle states that all users should log on with a user account that has the absolute minimum permissions necessary to complete the current task and nothing. What is the principle of least privilege (polp)? Web the principle of least privilege, or “least privilege access,” is a cyber security best practice that requires limiting users to the privileges necessary to perform a specific task. Web a minimum access policy ensures that users have the lowest level of privileges to complete necessary functions. The principle of least privilege access is a software security best practice that provides a user only the minimum set of rights required to perform an. Web the goal of least privilege enforcement is to give the user the least amount of privilege necessary to get their job done. Web developing an access termination policy for least privilege. Web blog what is least privilege & why do you need it? Web 19 jan 2022. Before using iam, it’s important to. In a least privilege model, privileged users and systems have. Web the principle of least privilege reduces risk by preventing people from having more access than they need. Before using iam, it’s important to. Web developing an access termination policy for least privilege. Web blog what is least privilege & why do you need it? Web the information security principle of least privilege asserts that users and applications should be granted access only to the data and operations they require to. Web applying the principles of least privilege aws identity and access management (iam) is the service used to manage access to aws services. In a least privilege model, privileged users and systems have. Web the goal of least privilege enforcement is to give the user the least amount of privilege necessary to get their job done. Web follow the principle of least privilege to implement a zero trust security strategy never grant broad or standing privileges. Web 19 jan 2022. Web the principle of least privilege, or “least privilege access,” is a cyber security best practice that requires limiting users to the privileges necessary to perform a specific task. Web this guide explains the principle of least privilege features and how to implement of principle of least privilege (polp). In this post, i’ve shown two different techniques that you can use to create least privilege policies for iam. Web a minimum access policy ensures that users have the lowest level of privileges to complete necessary functions. Best practice guide to implementing the least. They are based on compliance requirements outlined by cis, nist, pci and. Web the principle of least privilege model (also called the principle of minimal privilege or the principle of least authority) is widely considered to be a cybersecurity.PPT Lecture 17 Software Security PowerPoint Presentation, free
PPT IS3340 Windows Security Unit 2 Setting up Windows Systems with
PPT Security Principles and Practice PowerPoint Presentation, free
Principle of least privilege examples & best practices
PPT Lecture 10 Security Design Principles PowerPoint Presentation
PPT Secure Software Development PowerPoint Presentation, free
PPT Chp . 8 ISP Responsibility PowerPoint Presentation, free
8 Tips to Train Your Staff and Employees for Cybersecurity
Enforcing principle of least privilege
The 5 Most Important Strategies of the Security Principle of Least
What Is The Principle Of Least Privilege (Polp)?
Web The Principle Of Least Privilege Must Be Followed.
You Can Adapt These Methods.
Best Practice Guide To Implementing.
Related Post: