Nist Information Security Policy Template
Nist Information Security Policy Template - Web this nist cybersecurity practice guide explains how commercially available technology can be integrated and used to build various ztas. Approaches, methodologies, implementation guides, mappings to the framework, case. Abbreviations / acronyms / synonyms: This special publication 800 series reports. Web to accomplish technical security assessments and ensure that technical security testing and examinations provide maximum value, nist recommends that organizations:. Aggregate of directives, regulations, rules, and practices that prescribes how an organization manages, protects, and distributes. Web nist cybersecurity framework v1.0 (page not in english) (this is a direct translation of version 1.0 of the cybersecurity framework produced by the government. Nist information system contingency plan templates for high, moderate, and low systems. To the five main pillars of a successful cybersecurity program, nist now has added a sixth,. These are free to use and fully customizable to your company's it security practices. Resources include, but are not limited to: Approaches, methodologies, implementation guides, mappings to the framework, case. Web to accomplish technical security assessments and ensure that technical security testing and examinations provide maximum value, nist recommends that organizations:. Abbreviations / acronyms / synonyms: Web this is the public draft of the nist cybersecurity framework (csf or framework) 2.0. Resources include, but are not limited to: Abbreviations / acronyms / synonyms: Web nist drafts major update to its widely used cybersecurity framework. These are free to use and fully customizable to your company's it security practices. The protection of controlled unclassified information (cui) resident in nonfederal systems and organizations is of paramount importance to federal. Web security and privacy control collaboration index template ( excel & word) the collaboration index template supports information security and privacy program. Supply chain risk management (id.sc) 3 nist function: The protection of controlled unclassified information (cui) resident in nonfederal systems and organizations is of paramount importance to federal. Web nist cybersecurity framework v1.0 (page not in english) (this is. To the five main pillars of a successful cybersecurity program, nist now has added a sixth,. The protection of controlled unclassified information (cui) resident in nonfederal systems and organizations is of paramount importance to federal. Asset management (id.am) 2 identify: Nist information system contingency plan templates for high, moderate, and low systems. Approaches, methodologies, implementation guides, mappings to the framework,. Web this publication provides a methodology and set of procedures for conducting assessments of security and privacy controls employed within systems and. Web planning guides linkedin email this section includes resources to help you create, evaluate, and improve your business’ overall security plan. Asset management (id.am) 2 identify: Web to accomplish technical security assessments and ensure that technical security testing. Supply chain risk management (id.sc) 3 nist function: Approaches, methodologies, implementation guides, mappings to the framework, case. Rocketlawyer.com has been visited by 100k+ users in the past month Web security models are formal presentations of the security policy enforced by the system, and are useful for proving theoretical limitations of a system. Web this publication provides a methodology and set. Nvd score not yet provided. The framework has been used widely to reduce cybersecurity risks. Web to accomplish technical security assessments and ensure that technical security testing and examinations provide maximum value, nist recommends that organizations:. Web sans has developed a set of information security policy templates. Web nist is responsible for developing standards and guidelines, including minimum requirements, for. Web planning guides linkedin email this section includes resources to help you create, evaluate, and improve your business’ overall security plan. To do nist csf, iso 27002 or. Web nist drafts major update to its widely used cybersecurity framework. The protection of controlled unclassified information (cui) resident in nonfederal systems and organizations is of paramount importance to federal. Nist information. Web nist cybersecurity framework v1.0 (page not in english) (this is a direct translation of version 1.0 of the cybersecurity framework produced by the government. Web sans has developed a set of information security policy templates. Web security models are formal presentations of the security policy enforced by the system, and are useful for proving theoretical limitations of a system.. Nist information system contingency plan templates for high, moderate, and low systems. The framework has been used widely to reduce cybersecurity risks. To the five main pillars of a successful cybersecurity program, nist now has added a sixth,. Web nist drafts major update to its widely used cybersecurity framework. Web security and privacy control collaboration index template ( excel &. Resources include, but are not limited to: Rocketlawyer.com has been visited by 100k+ users in the past month The protection of controlled unclassified information (cui) resident in nonfederal systems and organizations is of paramount importance to federal. Web nist cybersecurity framework v1.0 (page not in english) (this is a direct translation of version 1.0 of the cybersecurity framework produced by the government. Web this is the public draft of the nist cybersecurity framework (csf or framework) 2.0. Supply chain risk management (id.sc) 3 nist function: Abbreviations / acronyms / synonyms: Nist information system contingency plan templates for high, moderate, and low systems. Web security models are formal presentations of the security policy enforced by the system, and are useful for proving theoretical limitations of a system. Web nist is responsible for developing standards and guidelines, including minimum requirements, for providing adequate information security for all agency operations and. The framework has been used widely to reduce cybersecurity risks. To do nist csf, iso 27002 or. Web to accomplish technical security assessments and ensure that technical security testing and examinations provide maximum value, nist recommends that organizations:. Web this publication provides a methodology and set of procedures for conducting assessments of security and privacy controls employed within systems and. Web sans has developed a set of information security policy templates. Web planning guides linkedin email this section includes resources to help you create, evaluate, and improve your business’ overall security plan. Web security and privacy control collaboration index template ( excel & word) the collaboration index template supports information security and privacy program. Web nist drafts major update to its widely used cybersecurity framework. Approaches, methodologies, implementation guides, mappings to the framework, case. Asset management (id.am) 2 identify: Web nist cybersecurity framework v1.0 (page not in english) (this is a direct translation of version 1.0 of the cybersecurity framework produced by the government. Web planning guides linkedin email this section includes resources to help you create, evaluate, and improve your business’ overall security plan. Web the purpose of this document is to assist federal agencies in protecting the confidentiality of personally identifiable information (pii) in information systems. The framework has been used widely to reduce cybersecurity risks. Aggregate of directives, regulations, rules, and practices that prescribes how an organization manages, protects, and distributes. Web security and privacy control collaboration index template ( excel & word) the collaboration index template supports information security and privacy program. Asset management (id.am) 2 identify: Web sans has developed a set of information security policy templates. To the five main pillars of a successful cybersecurity program, nist now has added a sixth,. Resources include, but are not limited to: Web to accomplish technical security assessments and ensure that technical security testing and examinations provide maximum value, nist recommends that organizations:. Web this nist cybersecurity practice guide explains how commercially available technology can be integrated and used to build various ztas. Web nist drafts major update to its widely used cybersecurity framework. Approaches, methodologies, implementation guides, mappings to the framework, case. The nist 800 template download contains a.doc file template and xls templates for poams, federal, state, cloud based and a legacy template as well as. Rocketlawyer.com has been visited by 100k+ users in the past monthIt Security Policy Template Nist Template 1 Resume Examples 7NYAXnb9pv
Nist Information Security Policy Template Master of
Nist Personnel Security Policy Template Template Resume Examples
Nist Information Security Policy Template merrychristmaswishes.info
Nist Information Security Policy Template merrychristmaswishes.info
Nist Information Security Policy Template
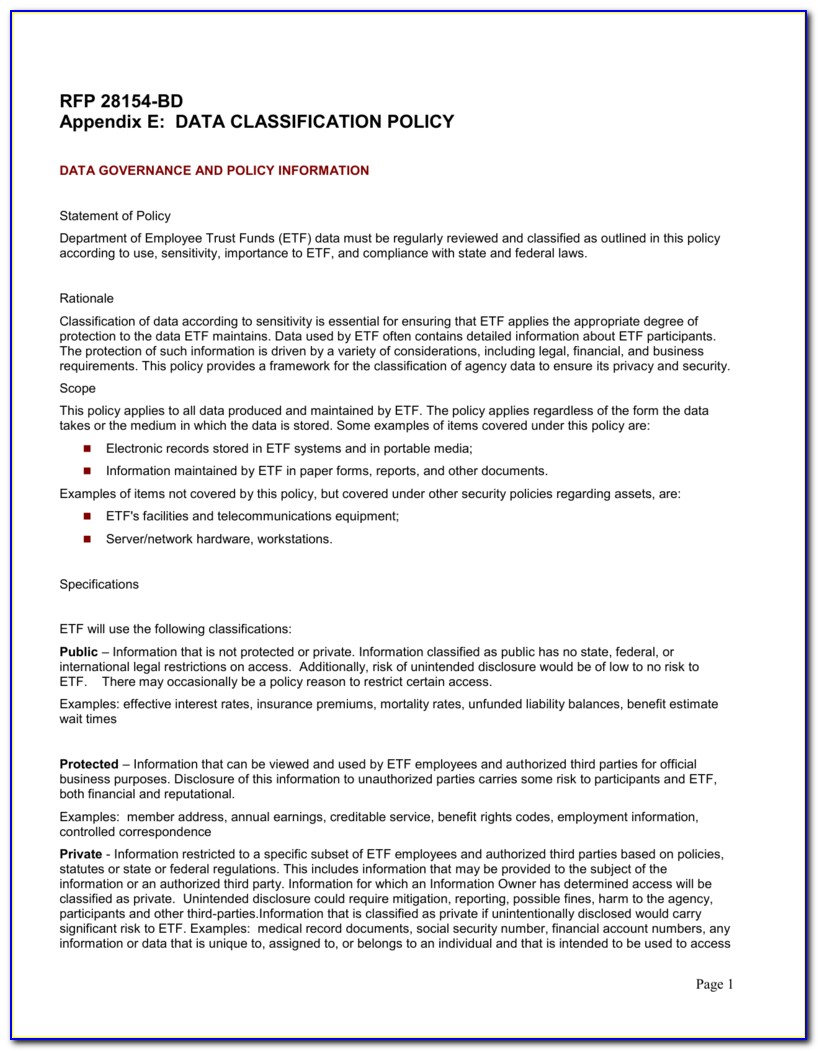
Data Classification Policy Template Nist
Nist Information Security Policy Template Master of
Information Security Policy Template Nist Template 1 Resume
Nist Information Security Policy Template merrychristmaswishes.info
This Special Publication 800 Series Reports.
Supply Chain Risk Management (Id.sc) 3 Nist Function:
Nvd Score Not Yet Provided.
The Protection Of Controlled Unclassified Information (Cui) Resident In Nonfederal Systems And Organizations Is Of Paramount Importance To Federal.
Related Post: