Threat Modeling Template
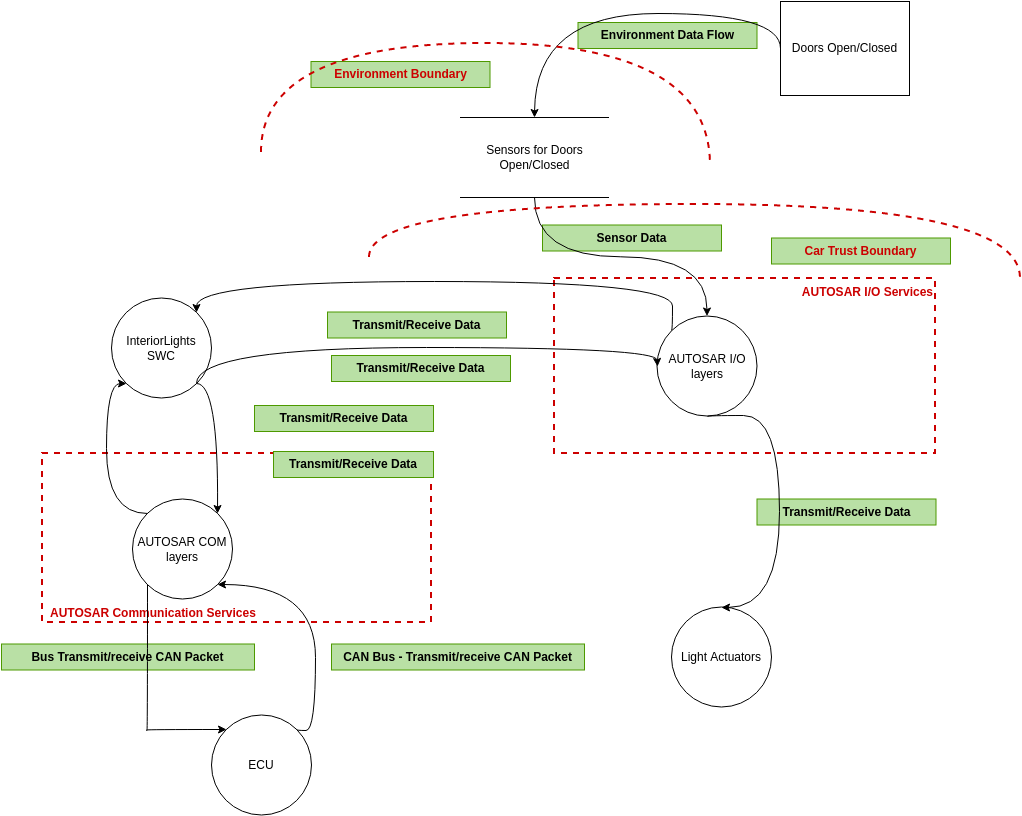
Threat Modeling Template - Web 102 threat modeling is a form of risk assessment that models aspects of the attack and defense sides of a 103 particular logical entity, such as a piece of data, an application, a. Web this document describes a structured approach to application threat modeling that enables you to identify, quantify, and address the security risks associated with an application. Threat dragon follows the values and principles of the. This report provides a survey of cyber threat modeling frameworks, presents a comparative assessment of the surveyed frameworks, and extends an existing. Web microsoft security development lifecycle threat modelling communicate about the security design of their systems. The basis of our threat modeling is modeled. Web we plan the following updates to our playbook (version 1.1) by end of 2022: Include a list of threat modeling methodologies. Web owasp threat dragon is a modeling tool used to create threat model diagrams as part of a secure development lifecycle. This delivery mechanism allows us to push the latest. Web threat modeling is a form of risk assessment that models aspects of the attack and defense sides of a particular logical entity, such as a piece of data, an. Threat dragon follows the values and principles of the. Web this document describes a structured approach to application threat modeling that enables you to identify, quantify, and address the security. Web microsoft security development lifecycle threat modelling communicate about the security design of their systems. This report provides a survey of cyber threat modeling frameworks, presents a comparative assessment of the surveyed frameworks, and extends an existing. Web threat modeling is a family of activities for improving security by identifying threats, and then defining countermeasures to prevent, or mitigate the. Web the threat modeling tool is a core element of the microsoft security development lifecycle (sdl). Identify and assign potential threats from. Create an architecture diagram and label the artifacts step 2: To open a blank page, select create a. Web we plan the following updates to our playbook (version 1.1) by end of 2022: To open a blank page, select create a. Create an architecture diagram and label the artifacts step 2: Web vast — vast (visual, agile and simple threat modeling) is a malleable and scalable modeling process for security planning throughout the software. Web the threat modeling tool is updated frequently, so check this guide often to see our latest features and. Web in this article. Include a list of threat modeling tools. Web we've developed an issue template available here (private link) that you can use to create an issue documenting your threat model. You must select which template to use before creating a model. Web we plan the following updates to our playbook (version 1.1) by end of 2022: Analyze those designs for potential security issues using a. To open a blank page, select create a. List down each architectural component step 3: Web vast — vast (visual, agile and simple threat modeling) is a malleable and scalable modeling process for security planning throughout the software. Include a list of threat modeling tools. This section provides the steps and results of a threat model analysis (tma) for each usage scenario for the sample architecture identified in sample. Identify and assign potential threats from. Web the threat modeling tool is a core element of the microsoft security development lifecycle (sdl). Include a list of threat modeling methodologies. Web owasp threat dragon is a modeling. Web threat modeling browse by category 4qs framework 5s 5w1h 5 whys 6s adkar aida funnel aws architecture diagram activity diagram affinity diagram alibaba cloud. Web we plan the following updates to our playbook (version 1.1) by end of 2022: Analyze those designs for potential security issues using a. This delivery mechanism allows us to push the latest. Include a. Identify and assign potential threats from. Web this document describes a structured approach to application threat modeling that enables you to identify, quantify, and address the security risks associated with an application. Web we plan the following updates to our playbook (version 1.1) by end of 2022: Web threat modeling browse by category 4qs framework 5s 5w1h 5 whys 6s. Include a list of threat modeling tools. The basis of our threat modeling is modeled. List down each architectural component step 3: Create an architecture diagram and label the artifacts step 2: Threat dragon follows the values and principles of the. This delivery mechanism allows us to push the latest. Web threat modeling browse by category 4qs framework 5s 5w1h 5 whys 6s adkar aida funnel aws architecture diagram activity diagram affinity diagram alibaba cloud. Web we plan the following updates to our playbook (version 1.1) by end of 2022: List down each architectural component step 3: Web in this article. It allows software architects to identify and mitigate. Web owasp threat dragon is a modeling tool used to create threat model diagrams as part of a secure development lifecycle. Threat dragon follows the values and principles of the. Web microsoft security development lifecycle threat modelling communicate about the security design of their systems. Web 102 threat modeling is a form of risk assessment that models aspects of the attack and defense sides of a 103 particular logical entity, such as a piece of data, an application, a. Analyze those designs for potential security issues using a. Web this document describes a structured approach to application threat modeling that enables you to identify, quantify, and address the security risks associated with an application. Web threat modeling is a structured approach of identifying and prioritizing potential threats to a system, and determining the value that potential mitigations would have in reducing or. Web vast — vast (visual, agile and simple threat modeling) is a malleable and scalable modeling process for security planning throughout the software. Web threat modeling is a family of activities for improving security by identifying threats, and then defining countermeasures to prevent, or mitigate the effects of, threats to the. The basis of our threat modeling is modeled. This section provides the steps and results of a threat model analysis (tma) for each usage scenario for the sample architecture identified in sample. Web threat modeling is a form of risk assessment that models aspects of the attack and defense sides of a particular logical entity, such as a piece of data, an. You must select which template to use before creating a model. Web we've developed an issue template available here (private link) that you can use to create an issue documenting your threat model. List down each architectural component step 3: Web the threat modeling tool is updated frequently, so check this guide often to see our latest features and improvements. Web vast — vast (visual, agile and simple threat modeling) is a malleable and scalable modeling process for security planning throughout the software. Web the threat modeling tool is a core element of the microsoft security development lifecycle (sdl). Web we plan the following updates to our playbook (version 1.1) by end of 2022: Create an architecture diagram and label the artifacts step 2: Web in this article. Analyze those designs for potential security issues using a. Web this document describes a structured approach to application threat modeling that enables you to identify, quantify, and address the security risks associated with an application. Threat dragon follows the values and principles of the. Include a list of threat modeling methodologies. This delivery mechanism allows us to push the latest. Web threat modeling browse by category 4qs framework 5s 5w1h 5 whys 6s adkar aida funnel aws architecture diagram activity diagram affinity diagram alibaba cloud. The basis of our threat modeling is modeled. To open a blank page, select create a. You must select which template to use before creating a model.The Automotive Threat Modeling Template NCC Group Research
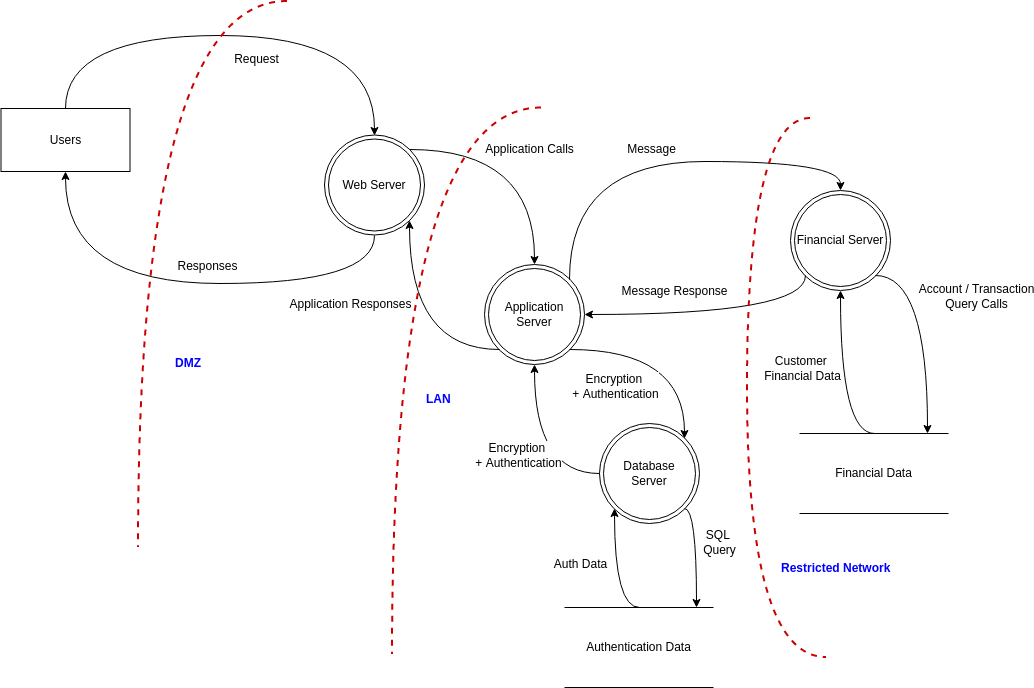
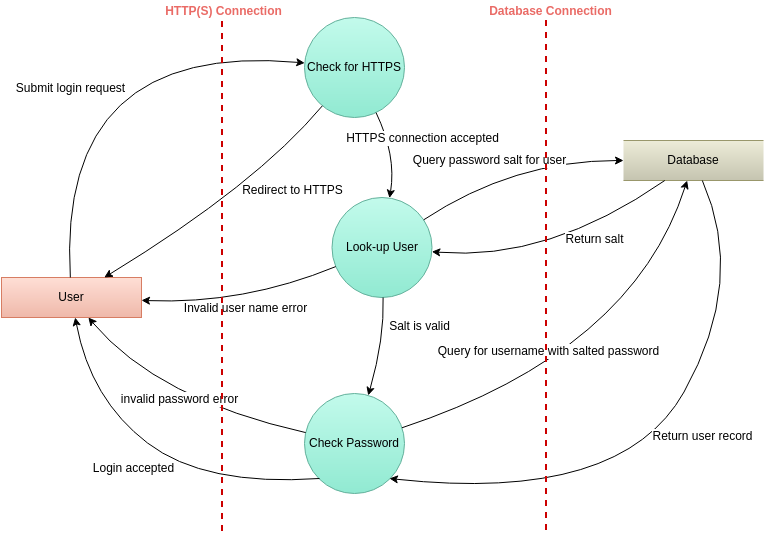
Website Threat Modeling Threat Model Diagram Template
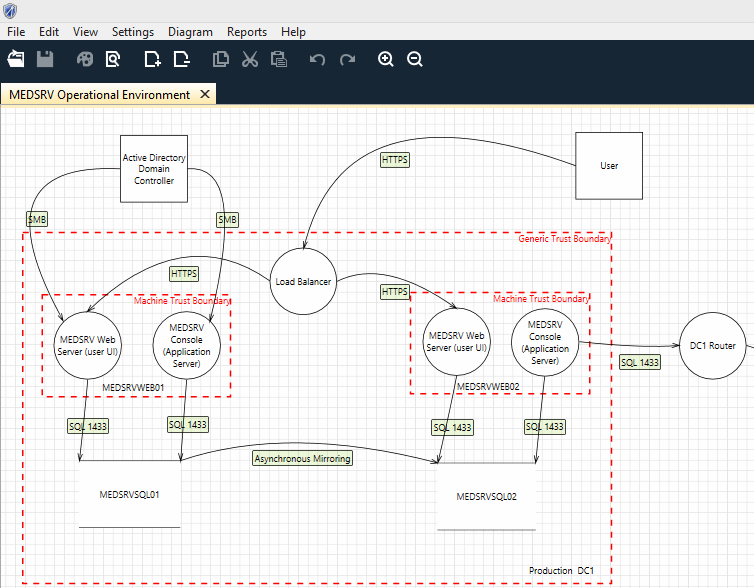
HolisticInfoSec™ toolsmith Microsoft Threat Modeling Tool 2014
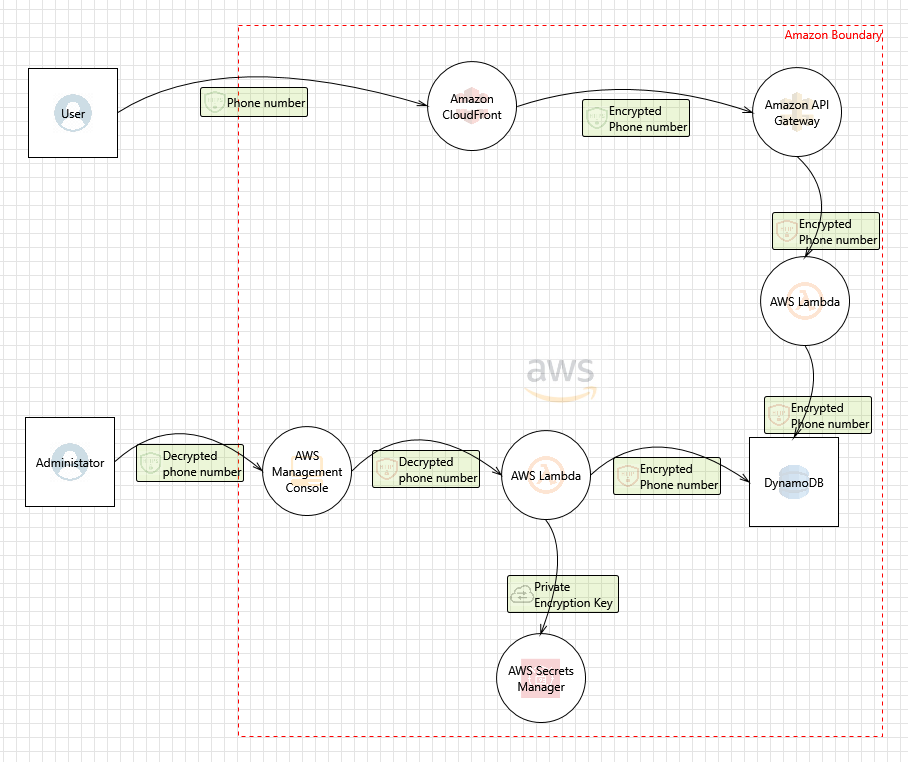
GitHub rusakovichma/awsthreatmodelingtooltemplate Amazon Web
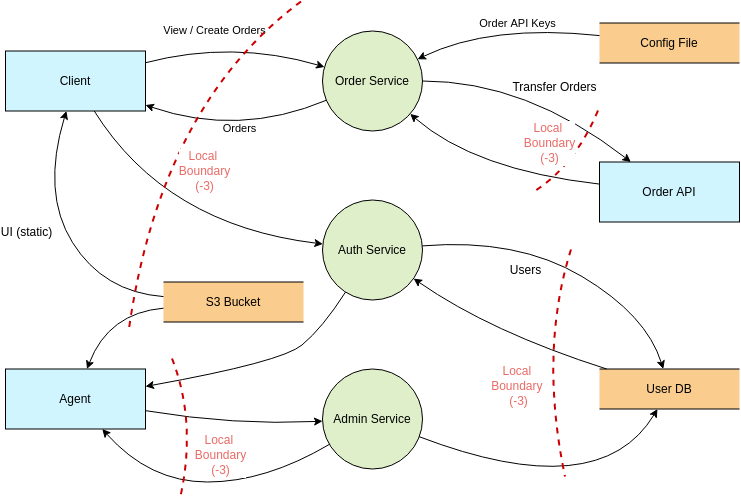
Threat modeling in the context of microservice architectures IBM
What Is Threat Modeling? (+Top Threat Model Examples)
GitHub AzureArchitecture/threatmodeltemplates Templates for the
Threat Risk Assessments 威胁模型图 Template
Threat Modeling Threat Model Diagram Template
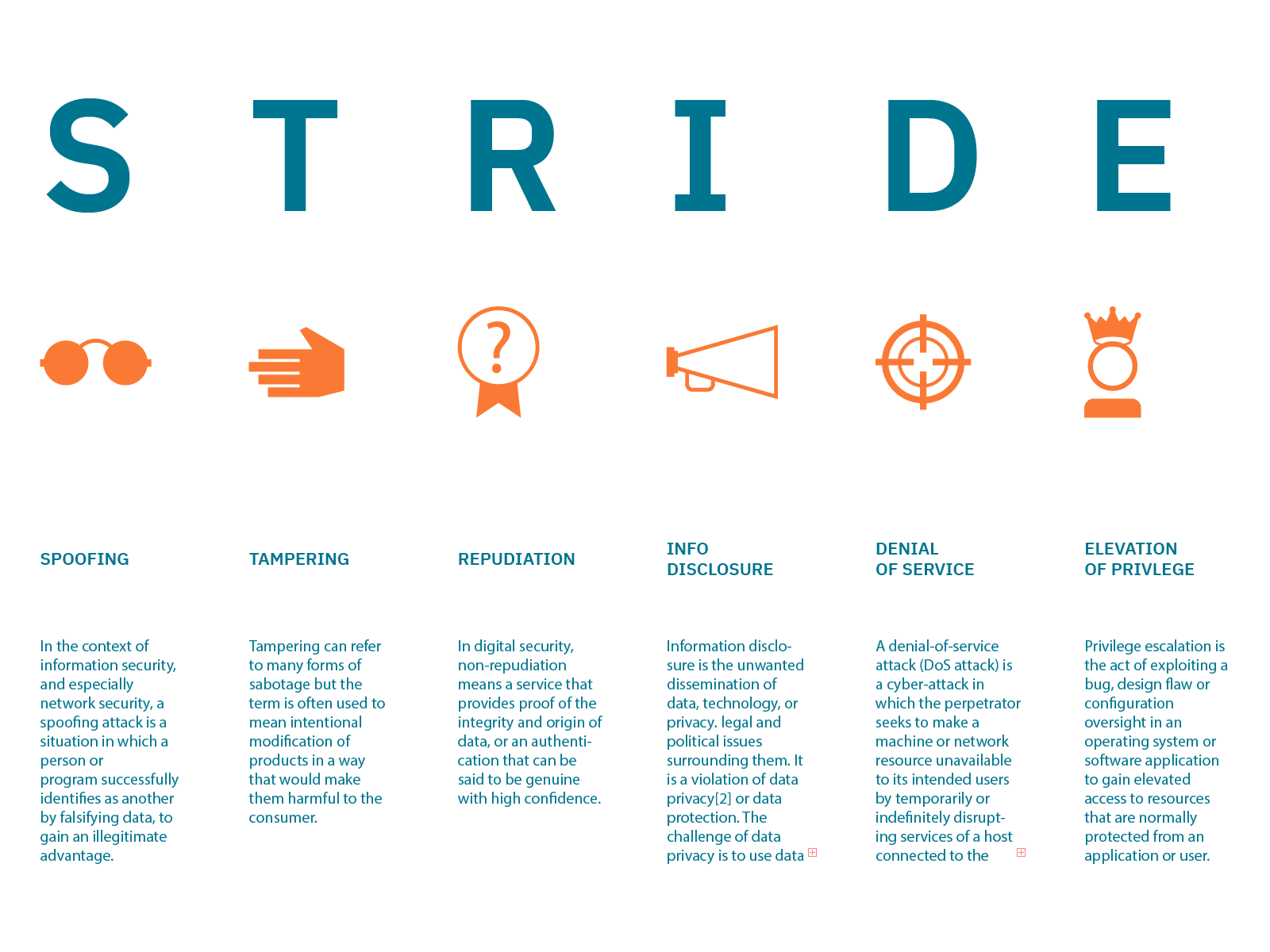
STRIDE Threat Model Threat Model Diagram Template
Web Owasp Threat Dragon Is A Modeling Tool Used To Create Threat Model Diagrams As Part Of A Secure Development Lifecycle.
Web 102 Threat Modeling Is A Form Of Risk Assessment That Models Aspects Of The Attack And Defense Sides Of A 103 Particular Logical Entity, Such As A Piece Of Data, An Application, A.
Web We've Developed An Issue Template Available Here (Private Link) That You Can Use To Create An Issue Documenting Your Threat Model.
Web Microsoft Security Development Lifecycle Threat Modelling Communicate About The Security Design Of Their Systems.
Related Post: